Cloud Access Security Broker (CASB)

Cloud Access Security Broker (CASB): Your Gateway to a Secure Cloud
The use of a wide variety of cloud models (SaaS, PaaS or IaaS) has become essential as the digital transformation has been gaining a foothold in the industry: Processes are being digitized and moved to the cloud. In addition, more and more software programs previously installed on end devices are now used as cloud solutions. But how can companies benefit from cloud solutions and their associated advantages without being exposed to security risks? These risks include uncertain access authorizations or the unintentional flow of data. It is critical to prevent sensitive company information such as secret or personal data from being downloaded onto a private end device or being transferred to unauthorized cloud applications. Another critical point is the uncertainty regarding data protection and compliance: As a company, you are obligated to adhere to compliance requirements not only in your own infrastructure, but also in the cloud.
The solution for these and other cloud security issues is the Cloud Access Security Broker (CASB). This complex software solution is kind of a control system that automatically detects risks in the cloud. As your independent partner, we provide completely neutral advice on which CASB is best for your specific needs, and support you during the implementation. This allows you to securely benefit from the advantages of the cloud such as agility and productivity.
Our claim is: Anytime, anywhere, any connection – always secure!
Always Secure: The CASB’s Most Valuable Services for Your Cloud Security.
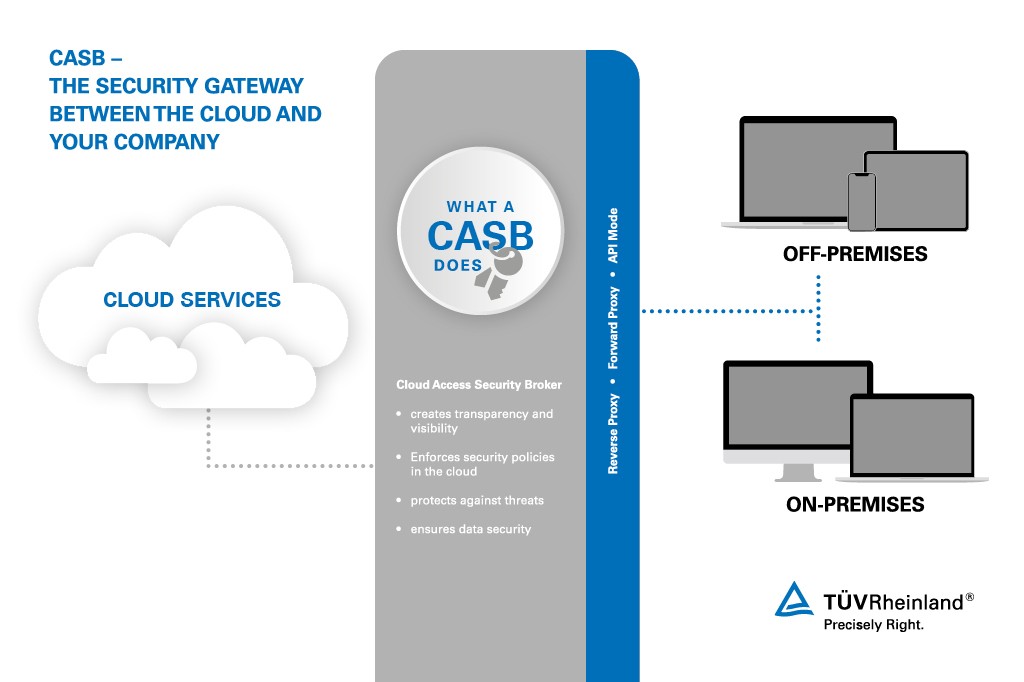
CASB is a service or application that monitors and logs data traffic between cloud applications and their users in real time. Based on the policies, CASB opens – or shuts – the door for connections between the cloud services and the users, like a highly specialized security service.
The CASB coordinates 4 main security areas:
- Visibility: Analyzing cloud usage creates transparency and visibility. The CASB analyzes which services are used and by whom. It also logs what data are uploaded or downloaded and their classification.
- Compliance: The CASB ensures that companies can implement their security policies not only within their own infrastructure, but also in the cloud. By enforcing security policies for access, authentication and encryption, the CASB increases the level of security.
- Protection from threats: The CASB monitors whether malware is lurking in your IT. It also detects when malware is moving from or to the cloud. It identifies anomalies that can be traced back to malware activity in cloud services.
- Data security: Since any access to applications in the cloud can be precisely controlled via the security guidelines, the CASB fends off unauthorized access attempts and thus protects against data loss. The CASB also defines policies, such as whether personal data may be stored unencrypted. The CASB also has an important function in the use of private end devices: it distinguishes private end devices from managed devices and can therefore also control and regulate different security policies when accessing business-critical cloud services. In addition, it prevents business-critical or sensitive data from being downloaded onto a private end device or being transferred to private cloud environments.
In addition to the security-related functions, the CASB also has monitoring and reporting functions. It analyzes your company's cloud usage and reviews the cloud providers' invoices. Your benefit: The reporting is helpful for planning capacity and the services necessary that users want from their IT departments.
With CASB, you can take advantage of all the benefits of the cloud without being exposed to security risks or having to accept limited functions.
Together for More IT Security
For the CASB to minimize the security risks from your cloud usage, certain prerequisites must be met. Your company must define what data are sensitive. It is necessary to establish a file classification and bring it to the awareness of the employees. Based on this classification, CASB identifies sensitive data and prevents their misuse.
As an independent consultant, we help you to find the right CASB solution for your company, to implement it and use it in your day-to-day business. We know the strengths and weaknesses of CASB solutions because we combine our recognized expert knowledge in the field of IT security with our industry expertise. On your path to cloud security, we will guide you and make sure that you achieve maximum productivity. Anytime, anywhere, any connection – always secure!
CASB is embedded in our Cloud Security Cycle; it is the most important building block in the "Protect & Detect" phase. Our consulting services begin with a needs assessment. This can also take the form of a shadow IT assessment .
Further topics
Our Sustainability Initiatives
Nothing less than the future is at stake. Companies, institutions, public authorities and each and every one of us can play a positive role in shaping the path to tomorrow. We provide you with comprehensive support to ensure that you operate safely, sustainably and efficiently for many years to come.
Contact






