Shadow-IT Assessment

Transparency about Cloud Services with our Shadow IT Assessment
Every day, new cloud services are developed that are freely available to companies and users, for example as Software as a Service (SaaS). Well-known SaaS applications that are also used in the business environment include Microsoft 365, Teams, Google Drive, Salesforce, ServiceNow and Zoom. The benefits of cloud services are evident: They can be used at any time, at any place and from almost any device, and therefore offer a very flexible way of working.
Many of these appealing cloud services are often not provided by corporate IT and therefore exist "in the shadows". Since they are not integrated into the security architecture, the usual security mechanisms of a company do not take effect – shadow IT is an enormous and often underestimated risk. Parallel to the rise of the cloud, the number of end devices with which employees access cloud services has been increasing as well. This also creates security gaps.
Our Shadow IT Assessment provides your company with transparency about the cloud services it uses. Based on the assessment, we will show you solutions to increase your IT security. Our claim is: Anytime, anywhere, any connection – always secure!
Shadow IT in Practice: What is the Problem?

It is essential to secure corporate data and to ensure compliant data handling. Shadow IT is one of the biggest risk factors and should therefore be addressed as a priority. We attach great importance to giving employees as much freedom and flexibility as possible while at the same time ensuring security. This is done by providing employees with secure alternative applications and at the same time use awareness training to make them aware of the risks
Stefan Graf, Cloud Security Expert at TÜV Rheinland.When employees download confidential company presentations to Dropbox so they can continue to work on them in the evening at home on their personal tablet, this can be a significant problem. What if the Dropbox account has been compromised? Is it allowed to upload these corporate data to a private Dropbox account? What happens when data flow into and out of the cloud? How do the different cloud services communicate with each other? Who is liable if data are lost or if customer data are not managed in a GDPR-compliant manner? Shadow IT results in companies not having an overview of the kind, number and usage of cloud apps outside of their own corporate IT tools, meaning their security measures are not effective. As a result, companies are also unable to take countermeasures if the shadow IT being used does not meet their own GDPR and compliance requirements.
Shadow IT can result in the loss and misuse of data, as well as in a breach of regulatory requirements. It poses a risk of losing the trust of your customers and of legal consequences.
How Does the Shadow IT Assessment Benefit Your Cloud Security?
An important step towards cloud security is to mitigate the risks associated with shadow IT. In the first step, the TÜV Rheinland Shadow IT Assessment provides visibility and transparency. Because only if you know the applications that are used can you secure them effectively. The Shadow IT Assessment is a cloud-based, semi-automated approach that identifies your company's unauthorized cloud services. It reveals those applications and highlights any risks.
This is what the Shadow IT Assessment does:
- It provides transparency about all SaaS services used.
- It qualifies and quantifies the risks your company may face from the use of these services.
- It provides details about each individual cloud service (who, when, how often, what amount of data).
- It audits cloud and web usage, taking into account compliance requirements.
Shadow IT Assessment: 4 Steps to an Overview and to Security
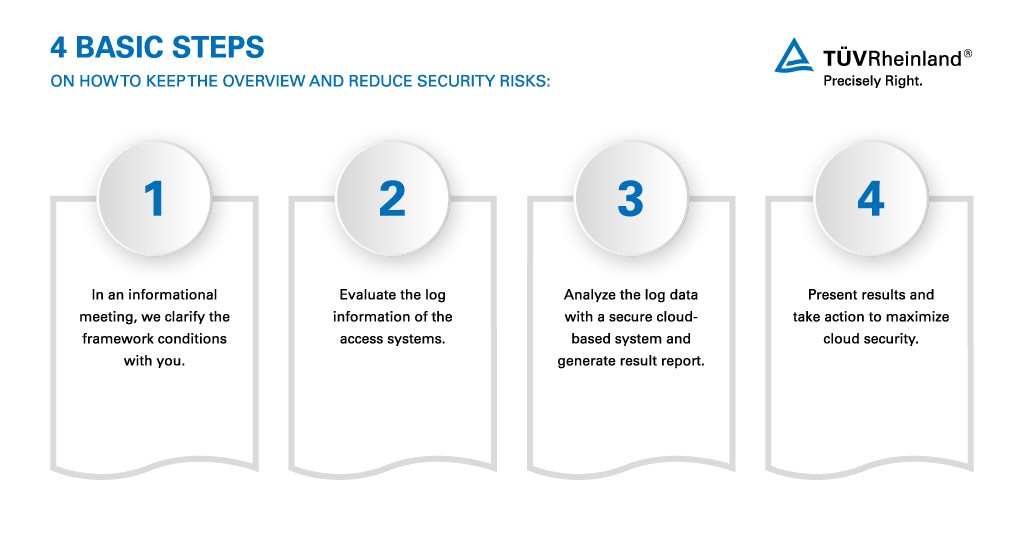
Our IT experts conduct the assessment together with you. We take your specific situation into account and tailor the assessment to the needs of your company.
Step 1: Informational meeting
In an informational meeting, we clarify the framework conditions with you. For example:
- What are the cloud services (e.g., Salesforce, Office 365) or cloud storage solutions approved by IT?
- Which of your company's data require special protection?
- What confidentiality policies (anonymization) are mandatory during the assessment and how should they be implemented?
- Which data governance or security policies require a special analysis?
Step 2: Access to your systems
During the assessment, we review the log information of the access systems (e.g., NG Firewall or Web Proxy) and will need the log data of the Internet breakout (NG Firewall, WebGateway, Proxy). We can process all log formats by the common firewall and proxy providers.
Step 3: Analysis and result report
For the analysis, our experts evaluate the log data using a secure cloud-based system, which processes the anonymized data automatically. The analysis takes two to four weeks and provides a complete overview of the cloud services used.
The results report will provide transparency on:
- Number and criticality of the services used
- Risk assessment of the used cloud services from the company's point of view
- Ratio between upload and download
- Which users (anonymized, if necessary) have the largest upload or download?
- Top 10 critical cloud services in terms of upload and download
- Top 10 critical cloud services in terms of number of users
- User-defined evaluations, if desired
Step 4: Consulting on consequences
We will present the results to you and advise and assist you in the next steps to effectively contain your shadow IT and to maximize your cloud security.
Foundation and Kick-off for Your Cloud Security
The Shadow IT Assessment is one of the first measures embedded in the Cloud Security Cycle. It can be conducted as a one-time assessment or be repeated regularly as a cycle. In any case, the assessment is a crucial milestone on the way to cloud security. This is because the transparency gained is an essential prerequisite for all steps that follow: to control and regulate cloud use, to adhere to data protection and compliance requirements, to enforce security guidelines and to ensure the security of corporate data. This is achieved with another important step in the Cloud Security Cycle: The Cloud Access Security Broker (CASB) – our complex software solution and your gateway to the secure cloud.
By using cloud applications securely, you fully benefit from the advantages of cloud services: You reduce your costs, gain flexibility and increase your productivity. At TÜV Rheinland, we actively support you – as a partner with recognized expertise and as an independent advisor. Anytime, anywhere, any connection – always secure!
Further Topics
Our Sustainability Initiatives
Nothing less than the future is at stake. Companies, institutions, public authorities and each and every one of us can play a positive role in shaping the path to tomorrow. We provide you with comprehensive support to ensure that you operate safely, sustainably and efficiently for many years to come.
Contact









