Challenges in the Identify phase:
- Missing and unclear security requirements
- Lack of clarity as to whether there is a reporting obligation in the event of a security incident
- Unclear if own company is affected by KRITIS regulation
- Lack of transparency about existing assets in own OT network
- Unclear threat situation
- - Cyber risks are not (yet) taken into account in holistic risk management
- Legacy systems in use that were developed without taking security threats into account represent an attack vector
- Complexity and disruption of new technologies
- Higher potential for digital fraud and damage to the operational process
- Safety-critical systems connected to potentially insecure bus systems
- Connectivity & openness of OT systems enable cyber attacks
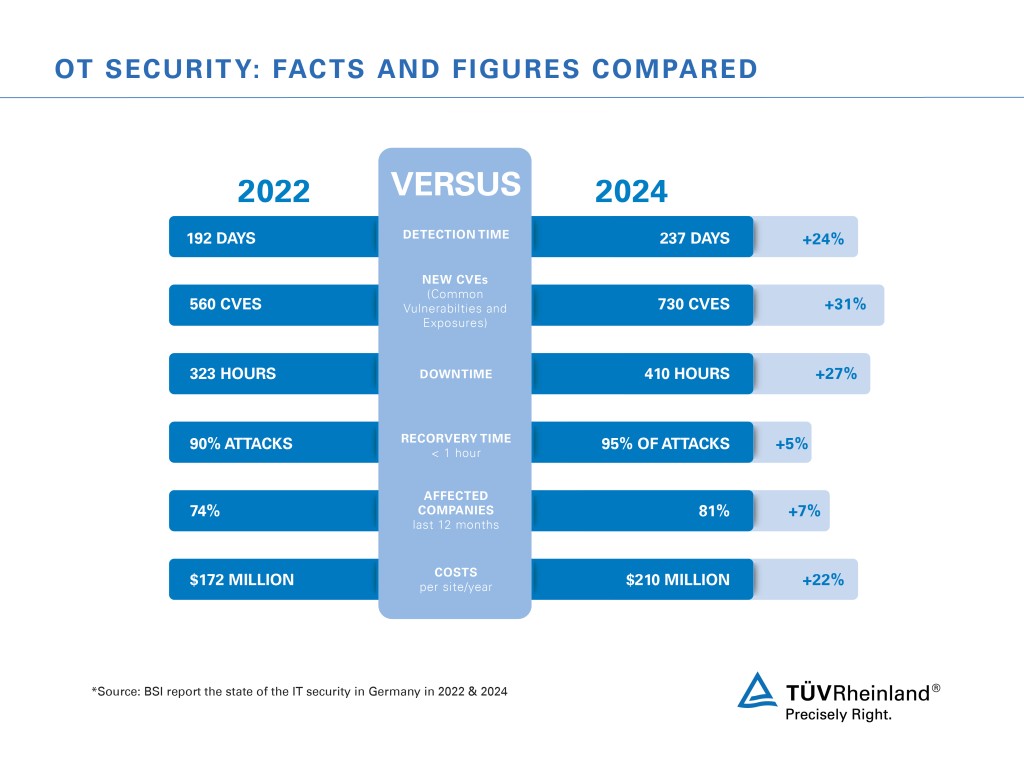
- Vulnerabilities and attacks are continuously increasing and becoming more sophisticated
Challenges in the Protect phase:
- Missing (security) concepts
- Inadequate architecture
- Missing processes
- Lack of integrated governance model and holistic risk management
- Lack of threat protection
- Unclear responsibilities regarding OT security (corporate vs. production IT)
- Failure to deal with the threat of digital fraud and damage to the operational process
- Protection against ransomware attacks
Solutions and Services
- Technical OT Monitoring
- OT Security Solution Design & Evaluation
- OT Remote Access / Maintenance Access
- Risk assessment / Risk evaluation
- Critical Infrastructure Consulting Critical Infrastructure Workshop OT-Security Awareness Training
- OT-Security Threat Modelling
- OT-Security Assessment
- OT-Security Solution Consulting
- Secure Digital Factory Architecture
-
Red & Blue Team Testing
- Identity Management
- Protection of Networks, Applications, Workloads, Endpoints
- Endpoint Detection and Response (EDR)
Challenges in the Detect phase:
- Missing implementations (technical, organizational, procedural solutions)
- Vulnerabilities and attacks are continuously increasing and becoming more advanced
- Legacy systems developed without consideration of security threats represent an attack vector
- Closed systems prevent the realization of security concepts and measures
- Limited detection capabilities in terms of zones/computers/systems (technical scope/depth of inspection)
- Ongoing shortage of specialists in the field of cybersecurity
Solutions and Services
- Technical OT Monitoring
- SOC Integration: OT Monitoring
- Vulnerability Assessment & Management
- Managed Threat Detection
- Anomalies and Events
- Detection processes
- Threat Intelligence
Challenges in the Respond phase:
- Lack of know how to deal with the threat
- Lack of experience in incident response
- No incident response process
- Unclear responsibilities / contact persons
- Ongoing shortage of cybersecurity professionals
Deployed legacy systems that were developed without consideration of security threats provide an attack vector
Solutions and Services
- Threat & Incident Response
- Response Planning
- Communication
- Analysis
- Mitigations
- Continuous Improvements
-
Digital Forensics
Challenges in the Recover phase:
- Lack of Business Continuity Management (BCM) and Detection & Response (DR).
- Lack of improvement process
- Lack of experience in continuous handling of BCM and DR cases
- Lack of clarity regarding communication strategy to stakeholders
- Unclear level of damage and recovery costs
 IT/OT convergence and complexity
IT/OT convergence and complexity
 Resilience
Resilience


 Protecting human life
Protecting human life
 Maintaining reputation
Maintaining reputation


 Data theft
Data theft
 Regulatory obligations
Regulatory obligations


 Skills shortage
Skills shortage
 Focus on CRA
Focus on CRA


-cybersecurity-services-1_core_2_2_1.jpg)
-cybersecurity-services_core_1_x.jpg)









