Web Application Firewall (WAF) Service

Make your web applications secure with our web application firewall services
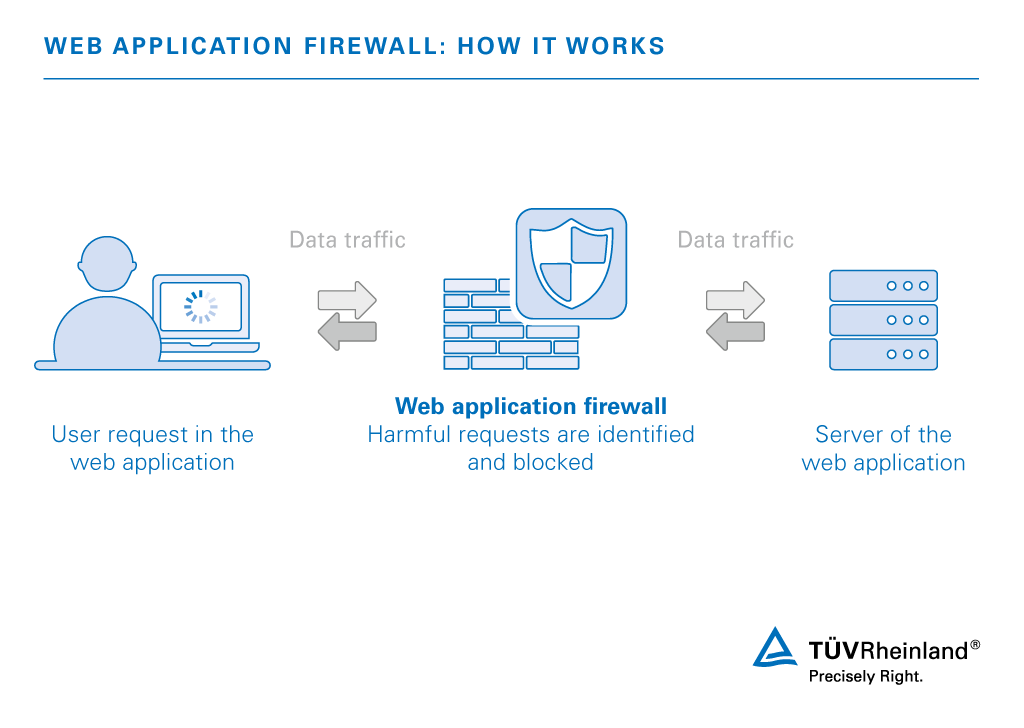
Web applications allow corporate applications to be used via the internet. As a result, they are often easy targets for hackers. This applies not just to traditional web services, but also to corporate applications such as Share Point, customer relationship management tools (CRM) and mail services. A web application firewall, or WAF for short, provides protection from attacks and control over data traffic without a need to modify the application itself.
Our experts assist you on your path to an effective web application firewall, from analyzing your existing systems to establishing an individual solution for your company.
As an experienced partner by your side we provide the right services for your company. That way you receive optimum protection for your web applications and their users. The service level is up to you: our offer ranges from modular assistance during operation to 3rd level support and a managed service.
Would you like to learn more about security for your web applications? Contact our experts now!
How a web application firewall protects your applications
Proactive protection for your web applications with the help of our WAF services
With assistance from our experts you reduce the security risks of your company’s web applications: analysis and implementation of the web application firewall provides you with proactive protection. You can obtain this security by means of our individual solutions, without laborious and costly modifications to your corporate applications. This in turn saves you time and money. The WAF also allows you to react quickly and automatically to vulnerabilities and attacks, so you protect your data and minimize your liability risk.
WAF: individual service – even during operation
A web application firewall protects web applications from attacks via the hypertext transfer protocol (HTTP). If suspicious content is identified while data is exchanged between clients and web servers, access is blocked by the WAF.
Over four phases, our experts help you achieve optimum operation of your web application firewall:
Phase 1: Analysis
We determine the security level of your application by examining the technology used and the data processed. We can also conduct a more thorough security analysis. This helps us identify existing vulnerabilities.
Phase 2: Design and product selection
Our experts work with you to plan the technologies that are most suitable as a web application firewall in your environment. We rely on our own product assessments, which we conduct regularly at our lab. We also test special requirements in your environment with a proof of concept (POC). If the project so requires, we also examine additional functions such as:
- Load distribution and reliability of your web application
- Encryption and optimization of the data flow
- Integration of authentication and permission control
- Integration of mobile end devices through secure and convenient authentication
- Single sign on (SSO) on different resources
Phase 3: Implementation
Our experts work with your employees to install the web application firewall in your productive environment – without impairing the operation of the web application. By this process, the WAF is integrated transparently and without modification of the network. The set of rules of the WAF can also be tested beforehand. We guide you through the process of rule creation and, if necessary, coordinate your contacts in application development and in the security and network team.
Implementation can take the form of a workshop. Your employees learn how to handle the system in practice and develop a deeper understanding of the functions.
Phase 4: Operation
Our experts assist you during the operating phase in order to maintain the security and availability of your application. We offer modular service-level agreements (SLAs), from 3rd level support to assistance with complex problems. The WAF can also be operated in the managed security service, so there is no need for you to train and provide additional employees.
Your competent partner for web application security
Benefit from the deep knowledge of our experts who offer effective solutions. Our modular SLAs are tailored to your individual needs – so support is always flexible and transparent in terms of cost.
Protect your web applications and use a web application firewall. Contact us and let our experts advise you!
Our Sustainability Initiatives
Nothing less than the future is at stake. Companies, institutions, public authorities and each and every one of us can play a positive role in shaping the path to tomorrow. We provide you with comprehensive support to ensure that you operate safely, sustainably and efficiently for many years to come.
Contact





