Information Security Strategy Consultation

Competent IT strategy consulting for information security
The security requirements for your company's information are steadily increasing. This is why a functioning safety management system is particularly important, as it functions as a decision-making base for implementing protective measures.
We offer comprehensive IT strategy consulting for information security. In the process, our experts help to create a consistent understanding from strategic decision to technical implementation. That way we can ensure a reliable and sustainable implementation of your safety measures.
As a provider of comprehensive solutions, we know we are the right partner for you. We apply solution requirements from the strategic information security level at your business to the technical level.
Benefit from our experience and knowledge. Contact us now to make an appointment with our experts.
Sustainable information security management through a comprehensive consultation
A strategy consultation with our experts will provide your company with a security strategy that meets its individual needs. Our solutions offer extensive and comprehensive security and are easy to implement in technical terms. There is also a special added value to our services: we offer cooperative assistance during the technical implementation that goes beyond strategic consultation.
Comprehensive solutions for complex information protection requirements
As a strategic adviser at eye level, we offer a comprehensive range of services – from analysis to solution for all safety-relevant, organizational, legal and technical questions:
- IT strategy consulting in the field of information protection
- Consulting services for compliance
- Risk management in the environment of information risks
- Auditing against in-house requirements or international standards
- Project management for organizational and technical implementations and standards (27001, ITIL®)
- Implementation of information protection
- Implementation of an ISMS according to ISO 27001 (organizational/technical)
- Consultation on safety standards as per DIN/ISO
- Awareness seminars
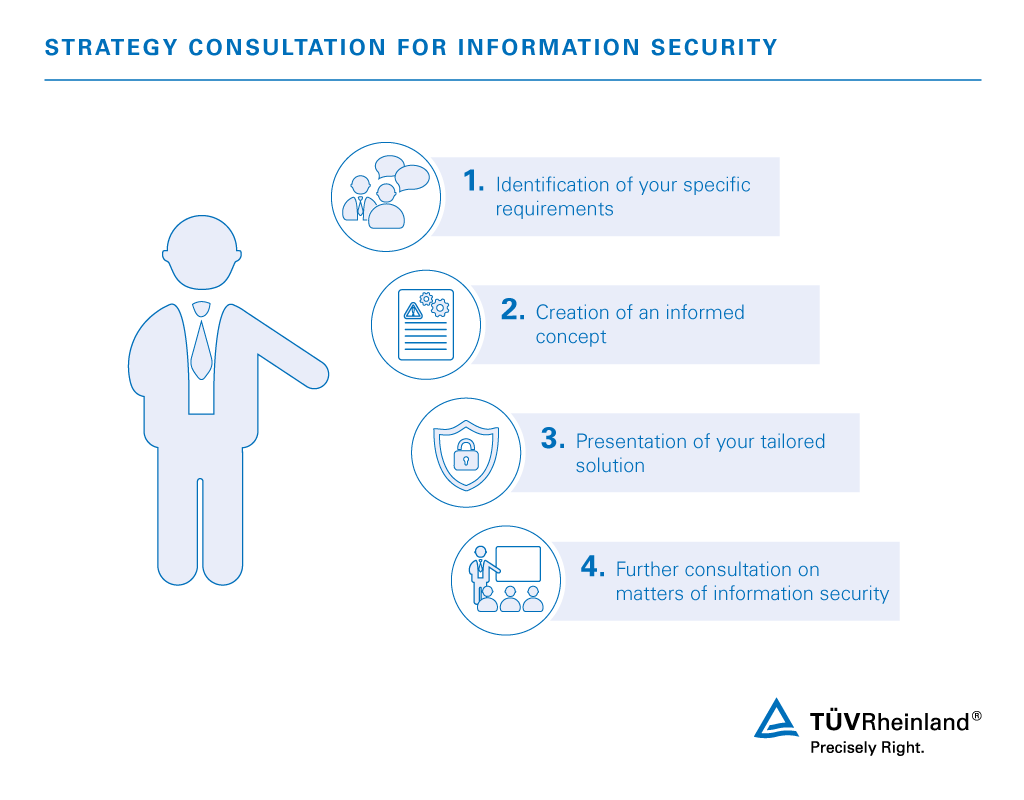
Our experts develop a comprehensive solution package for you and help you implement it in four structured steps:
- Workshop
In the workshop we define your specific requirements together. - Planning
We develop an informed concept for you based on our experience. - Implementation
We present you with a sustainable information security management system. When combined with your feedback, this process yields a tailored solution. - Consultation
Throughout every phase we are your collaborating advisor on all matters of strategic information security.
Information protection and IT security from experienced experts
Our experts have extensive experience in the field of IT strategy consulting. We implement strategic information security for you through individually designed and comprehensive solutions. We also collaborate in the technical implementation of these practical solutions.
Rely on our proven strategic problem-solving expertise and contact us now – for up-to-date IT security and information protection against threats.
Our Sustainability Initiatives
Nothing less than the future is at stake. Companies, institutions, public authorities and each and every one of us can play a positive role in shaping the path to tomorrow. We provide you with comprehensive support to ensure that you operate safely, sustainably and efficiently for many years to come.
Contact




/tuv-rheinland-external-ciso-chief-information-security-officer_core_4_3.jpg)
