Infrastructure as a Service (IaaS) and Platform as a Service (PaaS) are currently the most common delivery models for highly scalable operating environments. Companies purchase or lease resources such as computing power, development platforms or storage as a service and only pay for the resources they actually need and use (pay-as-you-go). IaaS and PaaS solutions are available from renowned providers such as Amazon Web Services (AWS), Microsoft Azure or Google GCP.
The benefits: Flexibility, scalability and cost. The limitation of capital investment (CapEx) has further accelerated the dynamic of these cloud services. By means of the cloud, IT is increasingly becoming an item of a service-oriented budgeting and billing cycle (OpEx).
The challenge for you as a company: You need to redefine the responsibility for infrastructure security and data security, as well as your service-level agreements.
These questions will help you do that:
- Where are the data stored or processed?
- Which legal framework applies at the storage location or the processing location (e.g., EU-GDPR)?
- Who ensures the 24/7 availability of the central services?
- Is there an effective disaster recovery concept in case of data loss?
- What regulatory and contractual measures need to be considered?
- Do the cloud service provider and the booked services meet the compliance requirements?
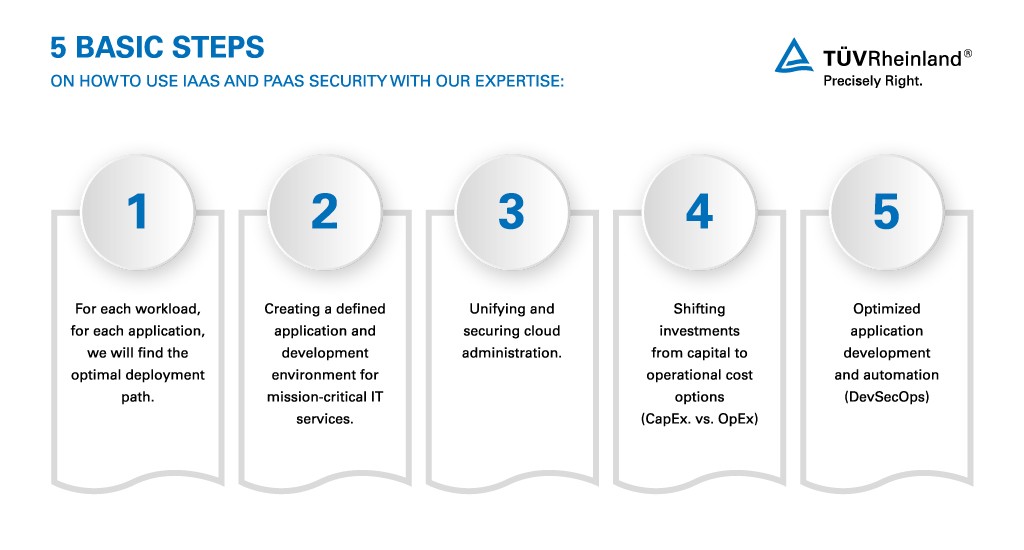
At TÜV Rheinland, we are your competent partner for the conceptual design and the secure operation of the most challenging IaaS and PaaS environments. Our consulting services, managed services and technology solutions help you choose precisely the right solutions for your needs. You avoid being dependent on individual providers (vendor lock-in) and remain flexible at all times, while at the same time optimizing budgeting parameters.
| Characteristics IaaS and PaaS | What challenges can arise for you from this? |
|---|---|
| Almost unlimited choice of the infrastructure and platform level used | The number of resources quickly becomes confusing and unmanageable. Resources used are not always configured in compliance with policies and thus may be insecure. |
| Cloud providers guarantee the availability of their own services and data security in the physical sense. | The shared responsibility model regulates responsibilities within the infrastructure. These differ between IaaS and PaaS services, whereby responsibility for data security, data protection (especially for personal data) and access rights always lies with the user. |
| The view of security is changing from secure perimeters to an application-centric or service-centric understanding of security with different security frameworks, data and legal spaces. | Complexity and gray areas in distributed responsibility or implementation open up new attack vectors for cyber attacks. In addition to physical data security, government intervention and different international legislations are coming to the fore. |
Cloud Security with TÜV Rheinland: Anytime, Anywhere, Any Connection – Always Secure
Cloud service providers are responsible for the security of their services to some extent. But even cloud providers are not always protected from unforeseen events such as fires or natural disasters. Still, as a business, you are ultimately responsible for ensuring that your data are secure and that you meet the applicable compliance requirements. The path to the resources, and the access to your systems must be secure. However, speed often takes precedence over security, because in their day-to-day business, employees do not accept systems that have long loading times due to complex security settings. There is a risk that users will switch to faster and thus less secure alternatives. We support you and provide you with solutions to ensure that you can use the advantages of IaaS/PaaS securely and with high access speeds.
As an independent partner, we advise and support our customers in advancing the digital transformation in their companies. Our interdisciplinary expertise from industry and IT security environment makes TÜV Rheinland a particularly qualified partner to verifiably increase the security of using cloud services. As a result, you as a company become more flexible, increase your productivity and reduce costs.
Consulting Services:
- Cloud Security Strategy
- Penetration Testing
- Secure Architecture
- Security Assessment
- Threat Modelling
- Data Protection Consulting
- Identity & Access Management
Managed Services & Technology Solutions:
- Cloud Security Posture Management (CSPM)
- Cloud Workload Protection Platform (CWPP)
- Cloud Access Security Brocker (CASB)
- Cloud Threat Detection & Respond


