How criminal team play makes cyberattacks even more successful.
The world of cybercrime has recently reached a remarkable level of maturity, one that is characterized by an evolving organizational structure and the formation of alliances and partnerships between different players.
Organized criminal gangs as the main players

The 2023 TÜV Cybersecurity Study finds that the cyberattacks of the last twelve months were mainly carried out by organized criminal gangs. Large and medium-sized companies rate the threat posed by individual criminal groups as significantly higher than small companies. In a comparison between industries, the concern about cyberattacks by organized crime is greatest in the manufacturing sector: 67% consider it a moderate or major threat.
This demonstrates that it is not only companies and organizations that are forming cyber alliances. Organized cybercriminals too are increasingly working together to make their own attack efforts even more successful, to make as much money as possible, or to support political goals.
Dark marketplaces and politically motivated players
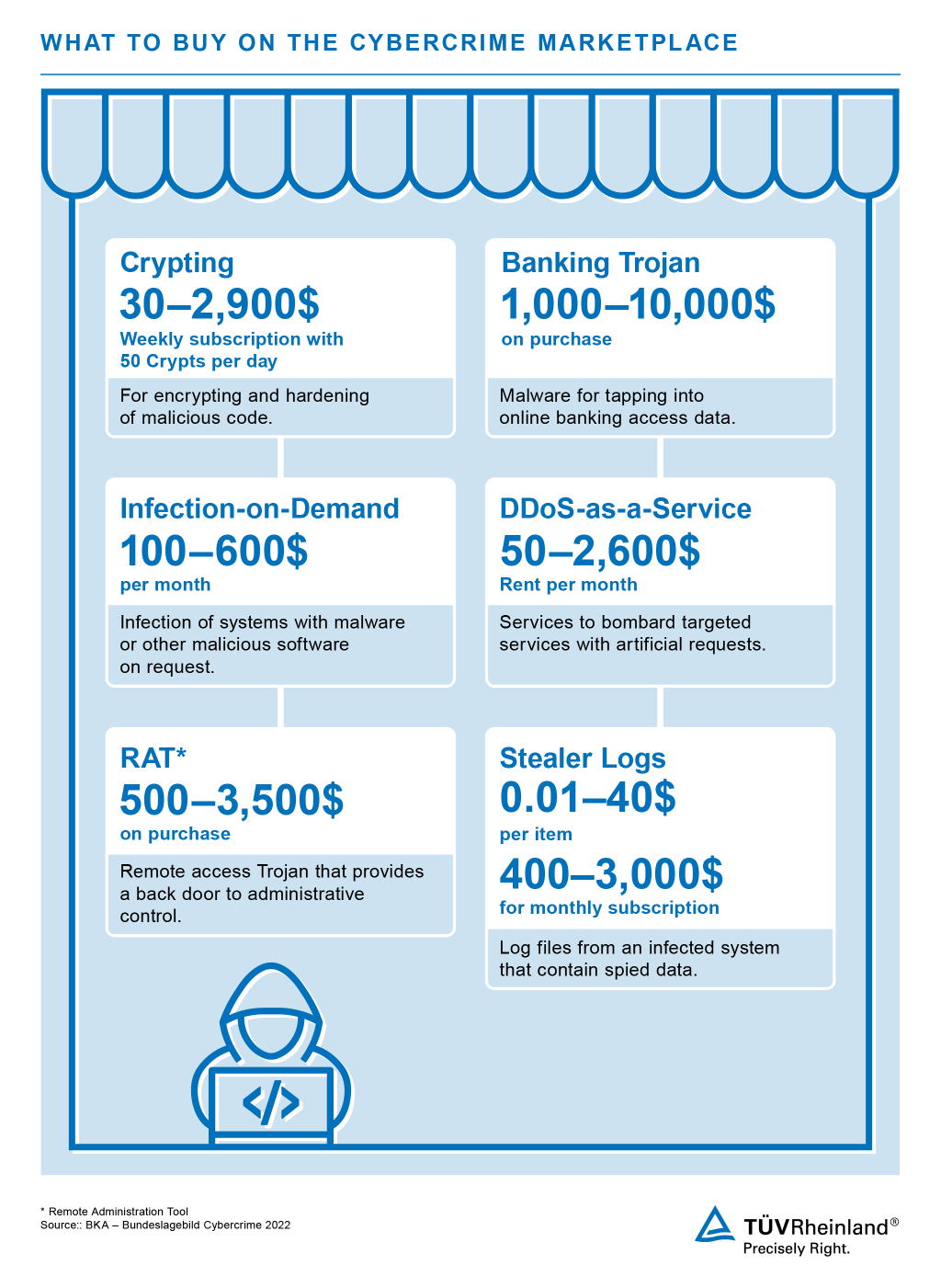
One of the central aspects of the underground economy (UE) are the cybercrime marketplaces on the darknet. This is where stolen identities, data, malware, exploit kits, and other illicit services are traded. These platforms enable cybercriminals to share or sell resources and expertise, creating the foundation for a wide range of criminal activities.
In some cases, it has been corroborated that even national governments are cooperating with cybercriminals to conduct covert operations to achieve their own political goals.
Situations like these have increased considerably in the wake of the overt government-induced attempts to influence the U.S. election campaign and since the beginning of the war in Ukraine. According to the BSI, the Russian war against Ukraine created a situation where for the first time in history a state with strong cyber capabilities is in an armed conflict with another digitized state. As a result, phenomena such as cyber espionage, hacktivism, disinformation campaigns, and cyber sabotage have increased dramatically.
Cybercrime-as-a-Service (CaaS)

The service sector has also long since entered the digital underworld. Cybercrime-as-a-Service (CaaS) allows even people with limited technical skills to carry out cyberattacks. Offerings such as Ransomware-as-a-Service or DDoS (Distributed Denial-of-Service)-as-a-Service are the most popular examples that represent the dangerous democratization of cybercrime.
Affiliate models allow even independent hackers to share in the profits. This is especially the case with ransomware attacks: By circulating the ransomware, the backers receive a share of the ransom obtained, which further significantly increases the reach and efficiency of the attack.
The underground economy (UE) is the primary marketplace and starting point for illegal goods and illegally obtained data, such as compromised payment data and access information, as well as for a wide variety of Cybercrime-as-a-Service offerings.
Increased division of labor and specialization
Another factor is the increasing specialization within cybercrime. While individual groups focus on specific areas such as network infiltration, data collection or the sale of that data, other teams take on different tasks such as executing the attack. This division of labor allows the players involved to operate even more efficiently and to maximize profits.
The sharing of infrastructure, such as botnets for DDoS attacks, and of command-and-control servers also shows how organized and coordinated cybercrime is today. All of this underscores the urgent need for organizations to continually adapt their security measures and to stay abreast of the changing threat landscape.
Don't give cybercriminals a target! Learn more about our cybersecurity services.
When it comes to your cybersecurity, there is no one-size-fits-all solution. That's why we offer you a flexible range of services – tailored to your individual needs and requirements.
Do you want to protect yourself against cybercriminal attacks? We're happy to help you!






